- Cisco ASDM features Quickly configure, monitor, and troubleshoot Cisco firewall appliances and service modules with this user-friendly application. Ideal for small or simple deployments, the Cisco Adaptive Security Device Manager offers.
- Oct 19, 2020 Download Cisco ASDM 10.10.20.4 from our website for free. Our built-in antivirus scanned this download and rated it as virus free. Cisco ASDM can be installed on 64-bit versions of Windows 7. The software lies within Security Tools, more precisely Antivirus. The program's installer is commonly called javaws.exe, asdm-launcher.exe or CiscoASDM.
Downloads Home; Search. Expand All Collapse All. My Notifications. Related Links and Documentation - No related links or documentation - Images.
Cisco Asdm Download Mac Os
Overview
Cisco ASDM-IDM Launcher is a Shareware software in the category Web Development developed by Cisco Systems, Inc..
The latest version of Cisco ASDM-IDM Launcher is currently unknown. It was initially added to our database on 08/16/2008.
Cisco ASDM-IDM Launcher runs on the following operating systems: Windows/Mac.
Users of Cisco ASDM-IDM Launcher gave it a rating of 3 out of 5 stars.
Write a review for Cisco ASDM-IDM Launcher!
| 11/03/2020 | iMyFone iBypasser 2.1.0.2 |
| 11/03/2020 | AweSun 1.5.0.30116 |
| 11/03/2020 | GSA Photo Manager 1.5.1 |
| 07/01/2011 | TBBackup 2.1.9 |
| 11/03/2020 | Webcam Video Capture 7.828 |
| 10/27/2020 | Firefox 82.0.1 update fixes causes of crashes |
| 10/26/2020 | New version of CCleaner available |
| 10/25/2020 | Kodi 18.9 release available |
| 10/23/2020 | Oracle updates fix 400 security vulnerabilities |
| 10/21/2020 | Adobe closes critical vulnerabilities in Photoshop and Illustrator |
- » asdm idm launcher windows 10
- » cisco ips idm 5.0 下载
- » cisco asdm-idm launcher java7
- » asdm-launcher скачать
- » cisco asdm windows インストール
- » cisco asdm launcher 7 скачать
- » download cisco asdm idm
- » descargar asdm todas las versiones
- » asdm idm launcher download
- » descargar cisco asdm
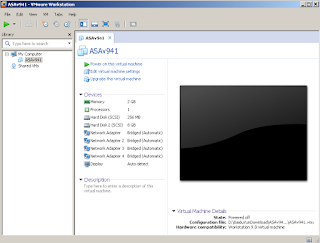
In this Video Tutorial I will show you how to enable initial access to the ASA device in order to connect with ASDM graphical interface or with SSH.
An out-of-the-box Cisco ASA device is not fully ready to be managed by the GUI interface (Adaptive Security Device Manager – ASDM). There is an initial configuration required to enable ASDM access to the firewall.
I know the above task in pretty basic but I hope it will help a few people that are just starting out with ASA firewalls.
Cisco Asdm 7.1 Download

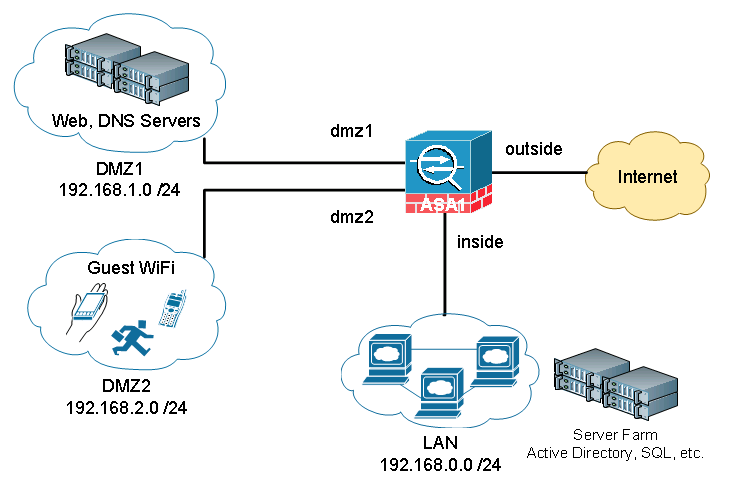
The network topology is shown below:
First we need to have console access (with a serial console cable) to the device in order to configure some initial settings to allow user access with ASDM or with SSH.
We will configure Interface GigabitEthernet 5 as a management interface with IP address 10.10.10.1/24.
Also, on the same subnet we have our management PC with IP address 10.10.10.10/24. The management PC is running also a TFTP server software (tftp32) which will be used to transfer the ASDM image to the ASA.
Below is the CLI configuration used in this initial setup (see video below also for more information):
ciscoasa# sh run
: Saved
:
ASA Version 8.4(2)
!
hostname ciscoasa
! Configure an “enable password” which is the administrator password of the device
enable password 2KFQnbNIdI.2KYOU encrypted
passwd 2KFQnbNIdI.2KYOU encrypted
names
!
interface GigabitEthernet0
shutdown
no nameif
no security-level
no ip address
!
interface GigabitEthernet1
shutdown
no nameif
no security-level
no ip address
!
interface GigabitEthernet2
shutdown
no nameif
no security-level
no ip address
!
interface GigabitEthernet3
shutdown
no nameif
no security-level
no ip address
!
interface GigabitEthernet4
shutdown
no nameif
no security-level
no ip address
!
! Configure IP address to Interface GigEth5 and put a high security level (90 is good).
! name also the interface as “management”
interface GigabitEthernet5
nameif management
security-level 90
ip address 10.10.10.1 255.255.255.0
!
ftp mode passive
pager lines 24
mtu management 1500
icmp unreachable rate-limit 1 burst-size 1
! Tell the appliance where the asdm image is located.
asdm image disk0:/asdm-647.bin
no asdm history enable
arp timeout 14400
timeout xlate 3:00:00
timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02
timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00 mgcp-pat 0:05:00
timeout sip 0:30:00 sip_media 0:02:00 sip-invite 0:03:00 sip-disconnect 0:02:00
timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute
timeout tcp-proxy-reassembly 0:01:00
timeout floating-conn 0:00:00
dynamic-access-policy-record DfltAccessPolicy
user-identity default-domain LOCAL
! SSH access will use the LOCAL username/password for authentication
aaa authentication ssh console LOCAL
! enable the HTTP service on the device so that you can connect to it for ASDM access
http server enable
! Tell the device which IP addresses are allowed to connect for HTTP (ASDM) access and from which interface
http 10.10.10.0 255.255.255.0 management
no snmp-server location
no snmp-server contact
snmp-server enable traps snmp authentication linkup linkdown coldstart warmstart
telnet timeout 5
! Tell the device which IP addresses are allowed to connect for SSH access and from which interface.
ssh 10.10.10.0 255.255.255.0 management
ssh timeout 5
console timeout 0
threat-detection basic-threat
threat-detection statistics access-list
no threat-detection statistics tcp-intercept
webvpn
! Configure a LOCAL username/password to be used for authentication.
username cisco password 3USUcOPFUiMCO4Jk encrypted
!
!
prompt hostname context
no call-home reporting anonymous
call-home
profile CiscoTAC-1
no active
destination address http https://tools.cisco.com/its/service/oddce/services/DDCEService
destination address email [email protected]
destination transport-method http
subscribe-to-alert-group diagnostic
subscribe-to-alert-group environment
subscribe-to-alert-group inventory periodic monthly
subscribe-to-alert-group configuration periodic monthly
subscribe-to-alert-group telemetry periodic daily
crashinfo save disable
Cryptochecksum:0760c72b39dd8d7a479d517a65758f33
: end
ciscoasa#
NOTE:
To enable SSH access, we need to generate also SSH keys as following:
ciscoasa(config)# crypto key generate rsa modulus 1024
Keypair generation process begin. Please wait…
ciscoasa(config)#
I have created the following video on youtube and thought about embedding the video here as well. It is about configuring the Cisco ASA in order to install the ASDM image (Adaptive Security Device Manager) and hence be able to manage the device with the graphical ASDM GUI.
The video shows also how to enable SSH access to the device, how to restrict access to a management network etc.
An out-of-the-box Cisco ASA device is not fully ready to be managed by the GUI interface (ASDM). There is an initial configuration required to enable ASDM access to the firewall.
Cisco Asdm Launcher
I know the above task in pretty basic but I hope it will help a few people that are just starting out with ASA firewalls.
Cisco Asdm Download Mac 10.10
Related Posts
